-
Resources
- Forums
-
The Future of Your Group Policy GPOs
We are sorry, the event "The Future of Your Group Policy GPOs" has already expired.
You may also be interested in.

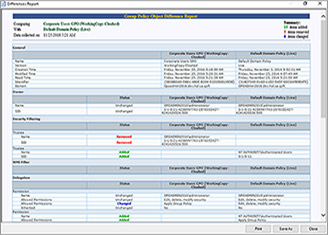
Three Key Ways to Improve Group Policy Management and Governance
Learn how to dramatically improve security while streamlining Group Policy administration with GPOADmin.
Read Technical Brief
Protecting Group Policy: Under Attack and Under the Radar
Protecting Group Policy: Under Attack and Under the Radar
Watch Webcast
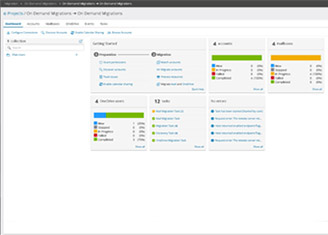
Group Policy Management - GPOADmin Demo
Watch this 30-minute demo where we'll cover how GPOADmin is a proxy-based administration and governance system for Group Policy.
Watch Webcast
Mitigating Active Directory threats before, during and after disaster
Identity, and Active Directory in particular, is a cyber attacker’s prime target, with 80% of breaches today involving compromised identities. From an attackers’ point of view, it makes se
Attend Event
TEC Talk: Microsoft Security Copilot – Potential, Hype, and Risk?
Learn to support IT organizations in strategy and implementation of security and compliance in digital transformation
Watch Webcast
TEC Talk: Abusing Group Policy for Fun and Profit
Group Policy is a systems management technology that can have great implications for the security of an Active Directory environment. In this session we will delve into the ways that GPOs can be both used and misused by those that gain a level of control.
Watch Webcast
TEC Talk: 5 Steps to Embark on Your Zero Trust Journey with Microsoft 365
Focus on securing identities, devices and applications, which are usually the first pillars to tackle in a Zero Trust journey. You will walk away with five projects that you can implement in your organization.
Watch Webcast